Get in touch with us. We will be glad to help you.
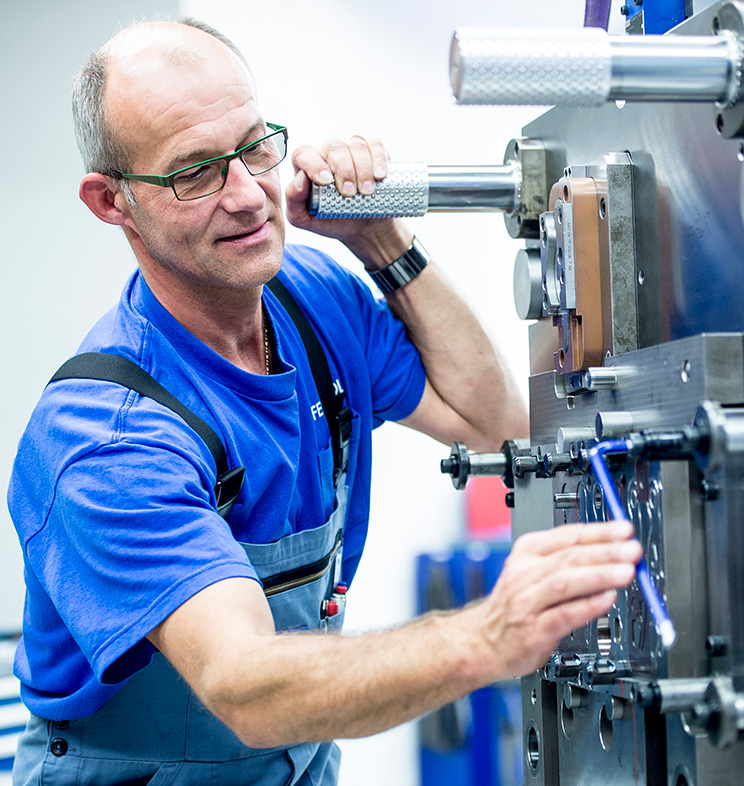
Based on our core technologies fineblanking, forming and electrolamination stamping, we offer unparalleled expertise in processing steel sheets and optimising manufacturing processes.

Advanced electric motors and components for various industry applications.
In today’s competitive engineering environment, quality and cost effectiveness while meeting specs & standards are key. We help you understand the options in detail and support you all the way with our knowledge and experience from the first calculations to the finished product.


We are happy to talk to you.
The Feintool Group
As an innovator in fineblanking, forming, and electrolamination stamping, we are shaping the technological world of tomorrow with an inimitable spirit of innovation at 17 locations worldwide – from high-performance fineblanking systems, tools, and manufacturing processes to the optimization of entire process chains, we are leading the way in transforming the future of technology today.


Contribute to our mission of “Expanding Horizons” and take your career to new heights with us: together, we will strengthen our position as the innovative global leader in fine metal processing. We are convinced that Feintool will become your first choice as an employer, and that you will be proud to be part of our team.
We operate at 17 locations in seven countries on three continents. Where would you like to work?
Apply now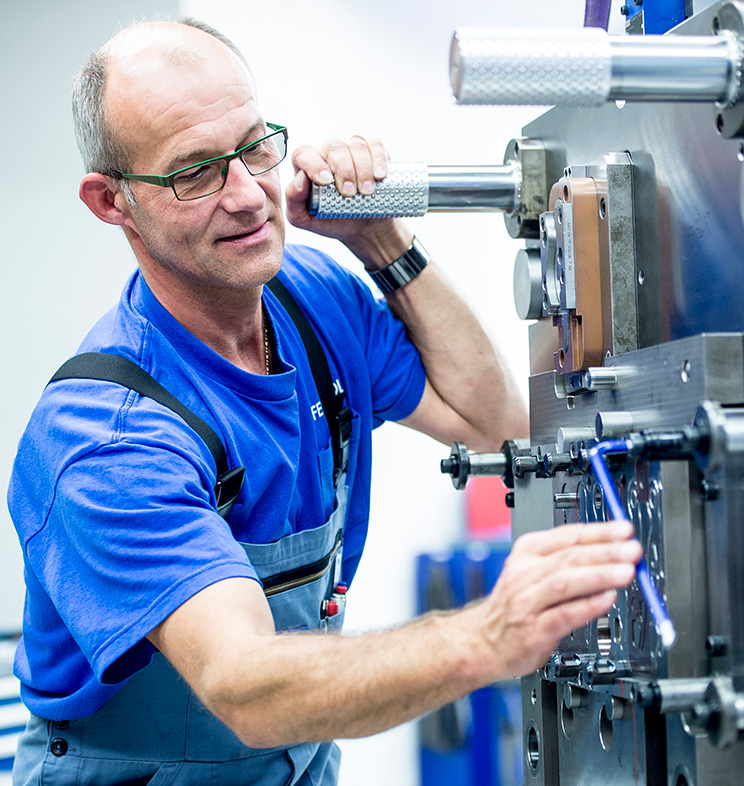
Get in touch with us. We will be glad to help you.